Do you want to obfuscate some sensitive data quickly and easily without having to go through the process of encryption? Look no further than ROT13. This simple command-line tool can help you obfuscate your data in a matter of seconds, making it difficult for others to understand without decoding it first. In this blog post, we’ll explore the ROT13 command in detail, including how to use it, its use cases, and frequently asked questions.
Prerequisites
Before we begin, make sure you have a basic understanding of the command line and how to run commands in the terminal. You should also have access to a Unix-based command-line interface, such as Terminal on macOS or PowerShell on Windows.
What is ROT13?
ROT13 (rotate by 13 places) is a simple encryption algorithm that replaces each letter in the alphabet with the letter 13 places ahead or behind it. It is a type of Caesar cipher, a technique named after Julius Caesar, who used it to communicate secretly with his generals. In ROT13, each letter is replaced with the letter that is 13 places away from it in the alphabet. For example, A is replaced with N, B with O, and so on.
How to Use the ROT13 Command
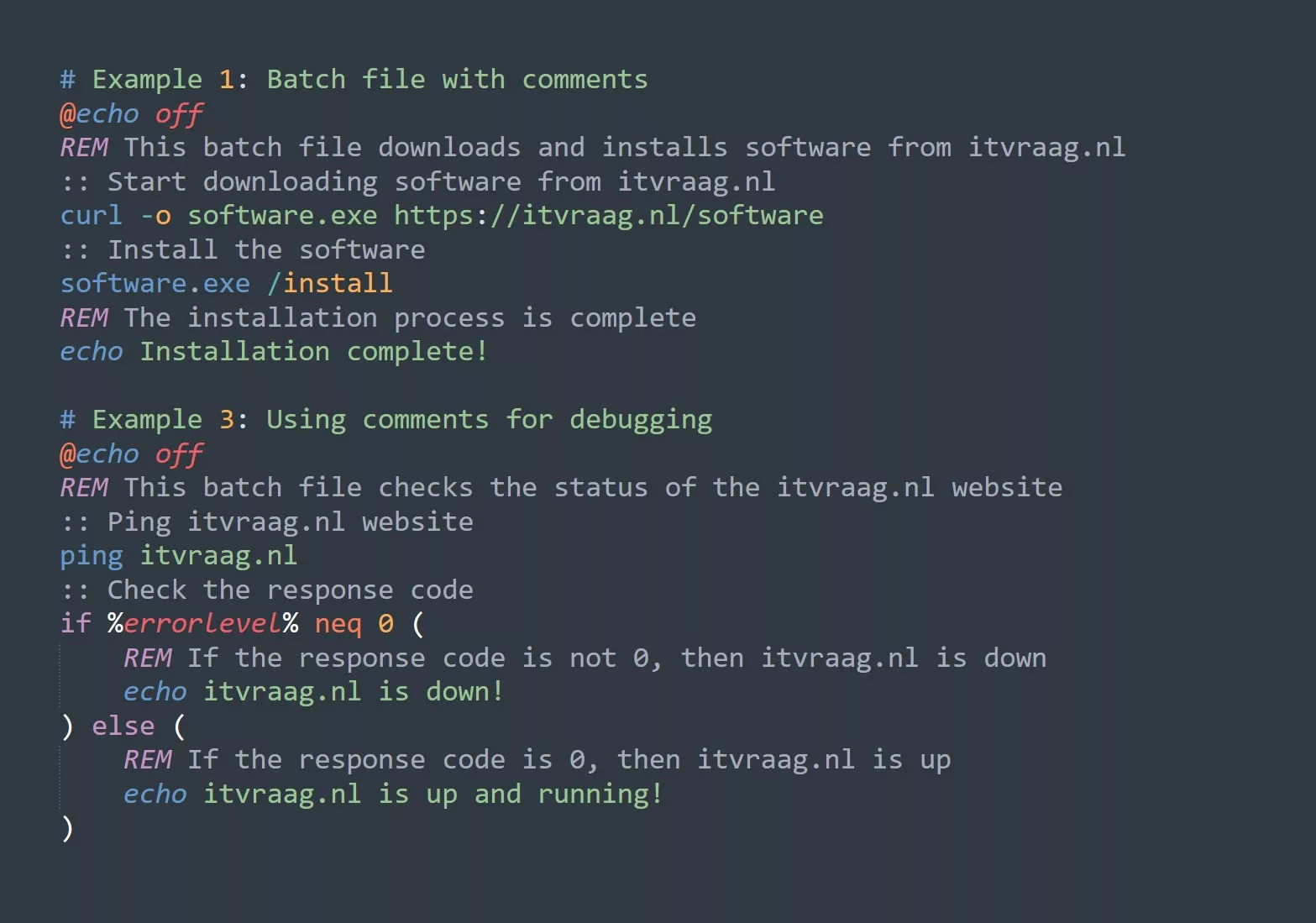
To use the ROT13 command, you can use the tr command, which is short for translate. The tr command is a standard Unix command that translates or deletes characters. The basic syntax of the command is as follows:
echo "your message here" | tr 'A-Za-z' 'N-ZA-Mn-za-m'
The echo command is used to print the message to the console, and the tr command is used to translate the message. The characters ‘A-Za-z’ represent all the alphabets, and ‘N-ZA-Mn-za-m’ represents the characters that will replace the original alphabets using ROT13.
ROT13 Cheat Sheet
| Task | Command |
|---|---|
| Encoding a message | echo “Welcome to itvraag.nl” |
| Decoding a message | echo “Jryyqbz gb vigine.tay” |
| Encoding a file | cat file.txt |
| Decoding a file | cat file-encoded.txt |
| Obfuscating data | echo “data” |
| Help | man tr or tr –help |
| Version | tr –version |
Use Cases for ROT13
Data obfuscation
ROT13 can be used to obfuscate sensitive data, such as email addresses, phone numbers, or login credentials. By obfuscating the data, it becomes more challenging for others to understand the information without decoding it first.
Email and password protection
ROT13 can be used to protect email addresses and passwords from being scraped by bots or hackers. By obfuscating the email address or password, it becomes more challenging for bots to recognize the data, making it more challenging to hack.
Learning tool for cryptography
ROT13 is an excellent tool for learning about cryptography and encryption. It is easy to understand and can be used as a stepping stone for more complex encryption techniques.
Frequently Asked Questions (FAQs)
Here are some frequently asked questions about ROT13:
What is the full form of ROT13?
ROT13 stands for “rotate by 13 places.” It is a simple encryption algorithm that replaces each letter in the alphabet with the letter 13 places ahead or behind it.
Is ROT13 secure for encrypting sensitive data?
No, ROT13 is not secure for encrypting sensitive data. It is a simple algorithm that can be easily decoded, and it should only be used for obfuscation and not encryption.
Can ROT13 be used for decrypting messages encrypted with itself?
Yes, ROT13 can be used for decrypting messages encrypted with itself. Since ROT13 is a symmetric encryption algorithm, the same algorithm can be used for both encryption and decryption.
Is ROT13 commonly used in modern cryptography?
No, ROT13 is not commonly used in modern cryptography. It is a simple algorithm that is not secure enough for modern cryptography, and there are many more advanced encryption algorithms available.
Conclusion
In conclusion, the ROT13 command is a simple yet effective tool for obfuscating data quickly and easily. It is not suitable for encryption but is perfect for obscuring sensitive data, such as email addresses and passwords. With a basic understanding of the command line and the ROT13 command syntax, you can start using ROT13 to protect your data today. If you have any further questions about ROT13, check out the FAQs or reach out to the IT community for further assistance.