Networking is a critical component of modern computing, enabling communication and data transfer between different devices and systems. Network protocols serve as the rules and standards that govern this communication, ensuring that data is transmitted accurately and reliably from one end to another.
In this blog, we’ll dive into the world of network protocols, exploring what they are, how they work, and why they’re so important.
What are Network Protocols?
At its core, a network protocol is a set of rules that define how data is transmitted over a network. These rules cover everything from the format of the data being sent, to the methods used to ensure that data is transmitted accurately and reliably, to the procedures used to handle errors and other issues that may arise during transmission.
Some of the most commonly used network protocols include TCP (Transmission Control Protocol), IP (Internet Protocol), and HTTP (Hypertext Transfer Protocol). These protocols are the building blocks that make it possible for us to use the Internet and other networks for tasks such as email, file sharing, and web browsing.
How do Network Protocols Work?
Network protocols work by breaking data into small, manageable packets, which are then transmitted over the network. At each step along the way, the receiving device checks the data against the network protocol rules to ensure that it’s correct and complete. If any errors are detected, the protocol provides a way to handle and correct them, ensuring that the data reaches its destination accurately.
For example, when you send an email, the message is broken into small packets and transmitted over the network using TCP. TCP ensures that the data is transmitted accurately by adding a checksum to each packet, which can be used to detect any errors that may occur during transmission. If any errors are detected, TCP will automatically request a retransmission of the affected packet, ensuring that the email arrives at its destination complete and accurate.
Why are Network Protocols Important?
Network protocols are essential for ensuring that data is transmitted accurately and reliably over a network. Without these protocols, communication between different devices and systems would be much more difficult and error-prone, leading to lost or corrupted data and other problems.
In addition, network protocols help to standardize communication between different systems, making it possible for them to work together seamlessly and efficiently. This is especially important for large-scale networks like the Internet, which must handle massive amounts of data from millions of devices and systems.
Examples
10 most popular network protocols, along with their place in the OSI (Open Systems Interconnection) model:
- HTTP (Hypertext Transfer Protocol) – HTTP is a protocol used for transmitting web pages and other content over the Internet. It operates at the Application layer of the OSI model.
- TCP (Transmission Control Protocol) – TCP is a reliable, stream-oriented protocol used for transmitting data over the Internet. It provides error detection and correction, ensuring that data is transmitted accurately. TCP operates at the Transport layer of the OSI model.
- IP (Internet Protocol) – IP is a network layer protocol responsible for routing data packets between networks. It operates at the Network layer of the OSI model.
- FTP (File Transfer Protocol) – FTP is a protocol used for transferring files over the Internet. It operates at the Application layer of the OSI model.
- DNS (Domain Name System) – DNS is a protocol used for converting domain names into IP addresses. It operates at the Application layer of the OSI model.
- SMTP (Simple Mail Transfer Protocol) – SMTP is a protocol used for transmitting email over the Internet. It operates at the Application layer of the OSI model.
- DHCP (Dynamic Host Configuration Protocol) – DHCP is a protocol used for automatically assigning IP addresses to devices on a network. It operates at the Application layer of the OSI model.
- ICMP (Internet Control Message Protocol) – ICMP is a protocol used for sending error messages and status information over the Internet. It operates at the Network layer of the OSI model.
- SSH (Secure Shell) – SSH is a protocol used for securely accessing remote computers over the Internet. It operates at the Application layer of the OSI model.
- SSL/TLS (Secure Sockets Layer/Transport Layer Security) – SSL/TLS is a protocol used for encrypting data transmitted over the Internet, providing a secure connection between two devices. It operates at the Transport layer of the OSI model.
Note that these protocols serve different purposes and operate at different layers of the OSI model, but all play a role in ensuring the smooth and secure transmission of data over networks.
Tcpdump Example
Here’s an example of a tcpdump output that illustrates the use of the HTTP, TCP, and IP protocols:
tcpdump: listening on en0, link-type EN10MB (Ethernet), capture size 65535 bytes
22:34:35.571222 IP 192.168.1.100.80 > 192.168.1.200.57216: Flags [P.], seq 0:52, ack 1, win 46, options [nop,nop,TS val 10208 ecr 1996432], length 52
E..4j@.@.@...........P.P.........
22:34:35.571307 IP 192.168.1.200.57216 > 192.168.1.100.80: Flags [.], ack 52, win 44, options [nop,nop,TS val 1996433 ecr 10208], length 0
E..4j1@.@.@...........P........
22:34:35.571957 IP 192.168.1.100.80 > 192.168.1.200.57216: Flags [P.], seq 52:104, ack 1, win 46, options [nop,nop,TS val 10208 ecr 1996432], length 52
E..4j@.@.@...........P.P.........
22:34:35.572023 IP 192.168.1.200.57216 > 192.168.1.100.80: Flags [.], ack 104, win 44, options [nop,nop,TS val 1996433 ecr 10208], length 0
E..4j2@.@.@...........P........
In this example, tcpdump is capturing packets transmitted between two IP addresses: 192.168.1.100 and 192.168.1.200. The packets are being transmitted over port 80, which is the default port for HTTP. The tcpdump output shows that data is being transmitted using the TCP protocol, as indicated by the Flags [P.] and Flags [.] lines, which represent TCP packets with the PUSH and ACK flags set, respectively. The IP protocol is also in use, as indicated by the IP addresses and the fact that the data is being transmitted over a network.
Practical Use-Cases
Network protocols are used in a wide range of applications, from everyday tasks like email and web browsing, to critical systems like financial transactions and medical data exchange. Some of the most notable use-cases include:
- Web Browsing: When you visit a website, your browser sends a request to the server using the HTTP protocol. The server responds with the requested information, which is then displayed in your browser.
- File Sharing: When you share a file with someone over a network, the file is broken into small packets and transmitted using the TCP protocol. This ensures that the file arrives at its destination complete and accurate, even if some of the packets are lost or corrupted during transmission.
- Email: When you send an email, the message is broken into packets and transmitted using TCP and IP protocols. These protocols ensure that the email is delivered accurately and reliably, even if some of the data is lost or corrupted during transmission.
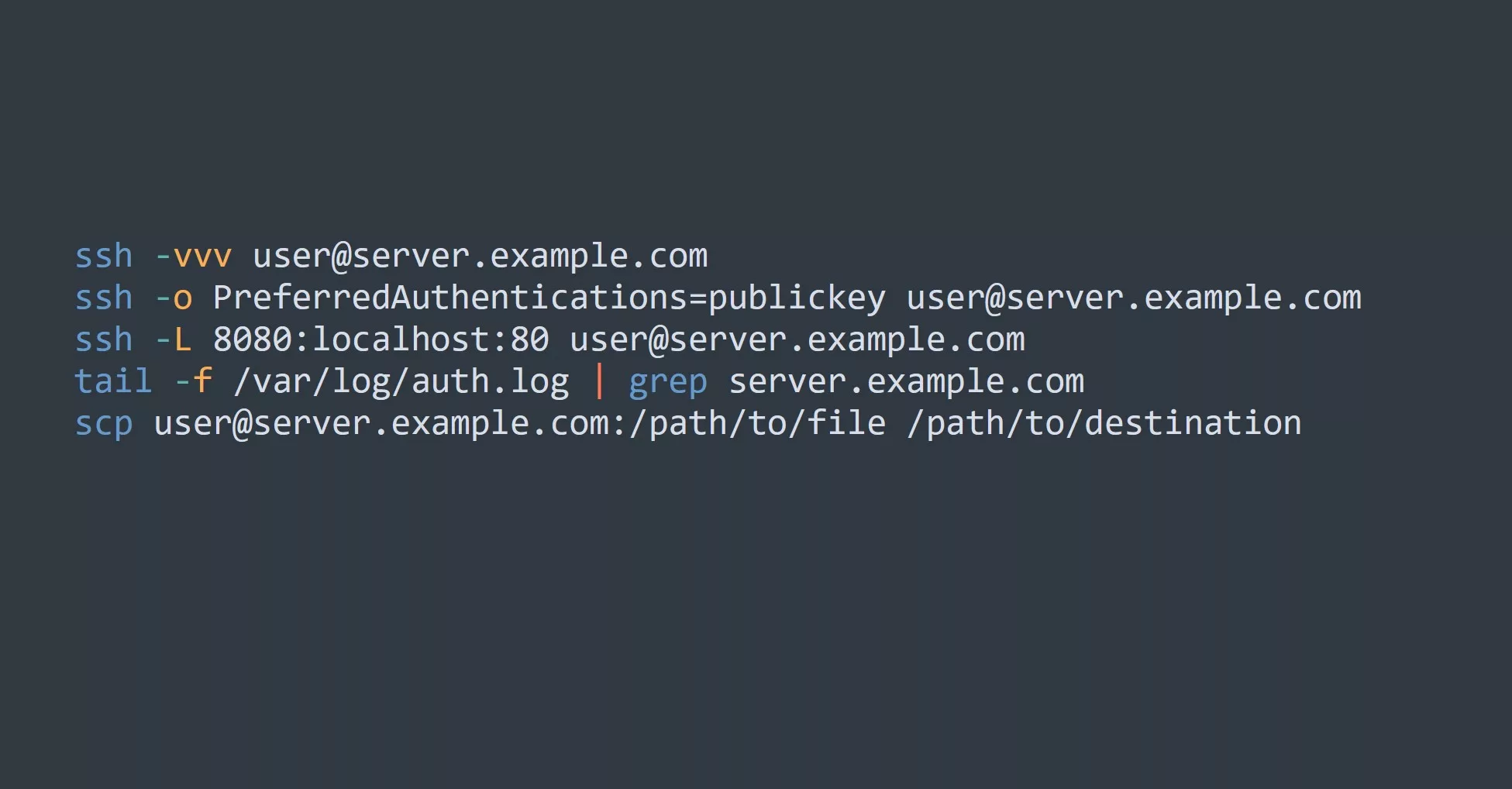
5 Tips for Power-Users and Advanced Users
- Familiarize yourself with the most commonly used network protocols, such as TCP, IP, and HTTP.
- Use network analysis tools like tcpdump and Wireshark to understand how data is being transmitted over a network.
- Configure your network devices to use the most appropriate protocols for your needs.
- Test the performance and reliability of your network by simulating different scenarios and testing the behavior of your network protocols.
- Keep up to date with the latest developments in network protocols and security, as these can impact the performance and security of your network.
Key Points
In conclusion, network protocols play a critical role in ensuring that data is transmitted accurately and reliably over a network. From web browsing and email to more complex applications like financial transactions, network protocols are the foundation of today’s connected world.
For those looking to further their knowledge of network protocols, we recommend exploring topics such as socket programming, data encryption, and network security.
Challenge
Try capturing tcpdumps on a Linux machine and analyze the output to understand different protocols being used. If you don’t have a Linux machine you can set one up easily on a Windows machine using WSL or Vagrant with Hyper-V.